Security Solutions
Optimize your IT security with the right solutions
Businesses today are constantly faced with new security threats. Protect your company from these threats with our customized Security Solutions. As a specialist for security solutions with years of practical experience, we plan and implement security concepts that fit your requirements exactly.
Our spectrum of services extends from analysis and evaluation of security and network infrastructure to the design of state-of-the-art security solutions to delivery and implementation. With Security Support and Managed Services, we support you in the secure operation of your infrastructure.
Our Security
Solutions Portfolio
In addition to the procurement of market and technology leading solutions, we offer a complete service portfolio for the analysis, planning, construction and operation of collaboration architectures:
Security audits & pentests
Security Audits & Pentests
Penetration Tests & Security Audits
ISO 27001 audit preparation
Risk analysis and assessment
Security Policies
Security strategy consulting
ISO 27001 consultung
Construction of an ISMS management system
IAM strategy, architecture and process consulting
Preparation for ISO 27001 certification
Security process consulting
External security officer
External data protection officer
Security awareness workshops
Security solution consulting
Selection of Security Solutions
Security architecture consulting
Economic efficiency studies
Security solution implementation
Project planning and management
Concept and design
Installation and configuration
Documentation
Coaching
Security support & managed services
Security support
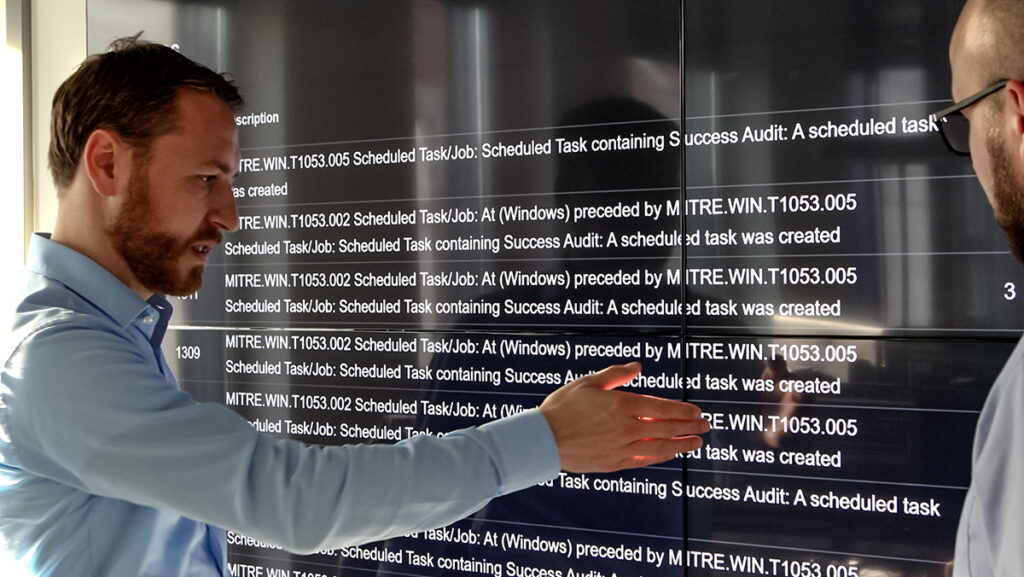
Security monitoring
Security management
Security as a service (SOC)
SOC as a Service
Security Incident response
Vulnerability monitoring
Our partners for the security sector
Contact
Talk to us about your project!
Contact us! Our experts will contact you quickly and will assist you.

